CipherStash blog
§ 00·0x00/FEATURED / READ FIRST
§ 01·0x01/ARCHIVE / ALL POSTS

Whose query is this?
Your agent's database connection knows the app, not the user behind the prompt. Identity-bound encryption closes the gap.

Field-level encryption in JavaScript: how to do it without shooting yourself in the foot
Ask an LLM how to encrypt a field in TypeScript and you'll get a working AES-GCM snippet — and a hidden pile of footguns around keys, modes, and ORM plugins. Here's what actually goes wrong, and how @cipherstash/stack avoids it on Node.js, Next.js, Cloudflare Workers, and Deno.

Adding CipherStash Stack to a Next.js + Supabase app
A short, code-heavy walkthrough — add searchable field-level encryption to a Next.js + Supabase app with CipherStash Stack. Both App Router and Pages Router. Stack-first; no Protect.js.

Encrypting Supabase data with CipherStash Stack
Drop-in field-level encryption for Supabase that keeps your queries working. Equality, LIKE, ranges and ordering — all over ciphertext, with the Supabase JS client you already use.

Searchable encryption in Postgres: a working guide with CipherStash Stack and EQL
Encrypt your data, keep the queries. A practical, indexable approach to searchable encryption in Postgres — 410,000× faster than fully homomorphic encryption — with a working code example using @cipherstash/stack and EQL.

CipherStash + Prisma Next: Data Level Access Control, declared in your contract
Add searchable field-level encryption to a Prisma Next app the same way you'd add any other field — declared once in your contract, evolved the same way.

One billion sensitive values encrypted in production
From a tough sell five years ago to over one billion encrypted values today — here's how CipherStash earned the trust of dev teams who were nervous about encrypting their most precious data.
Fixing a 1-in-256 bug in CLWW order-preserving encryption
Order-preserving encryption lets databases sort and range-query encrypted columns. A well-known 2015 scheme (CLWW) hints at a simple byte-compare trick for ordering ciphertexts — but it's wrong about 1 in 256 comparisons. Here's why, with a worked example, and two small encoding changes that eliminate the error.

You can certifiably trust us. Read on to find out why you don't need to!
While our shiny new SOC 2 Type 2 badge shows that you can trust us, if you're using CipherStash, you don't actually *need* to trust us. Your customers' sensitive data is always secure.

How we used the PostgreSQL wire protocol to bring you searchable encryption
When using CipherStash Proxy, applications can interact with encrypted data in a Postgres database as if it were plaintext. SQL statements are intercepted, parsed, type-checked, and mapped to the configuration specifying the types of encryption to use. In order to make all of this smart magic work to abstract the complexity of searchable encryption, CipherStash Proxy has to handle the nuances of the PostgreSQL wire protocol.

Rewriting SQL on the fly in CipherStash Proxy – part 1
CipherStash Proxy helps teams who need advanced data security controls but don't have the capability or capacity to make changes to their apps. With CipherStash Proxy, developers, devops engineers, and SREs can encrypt their most sensitive data in Postgres databases with zero changes to SQL queries in their apps.
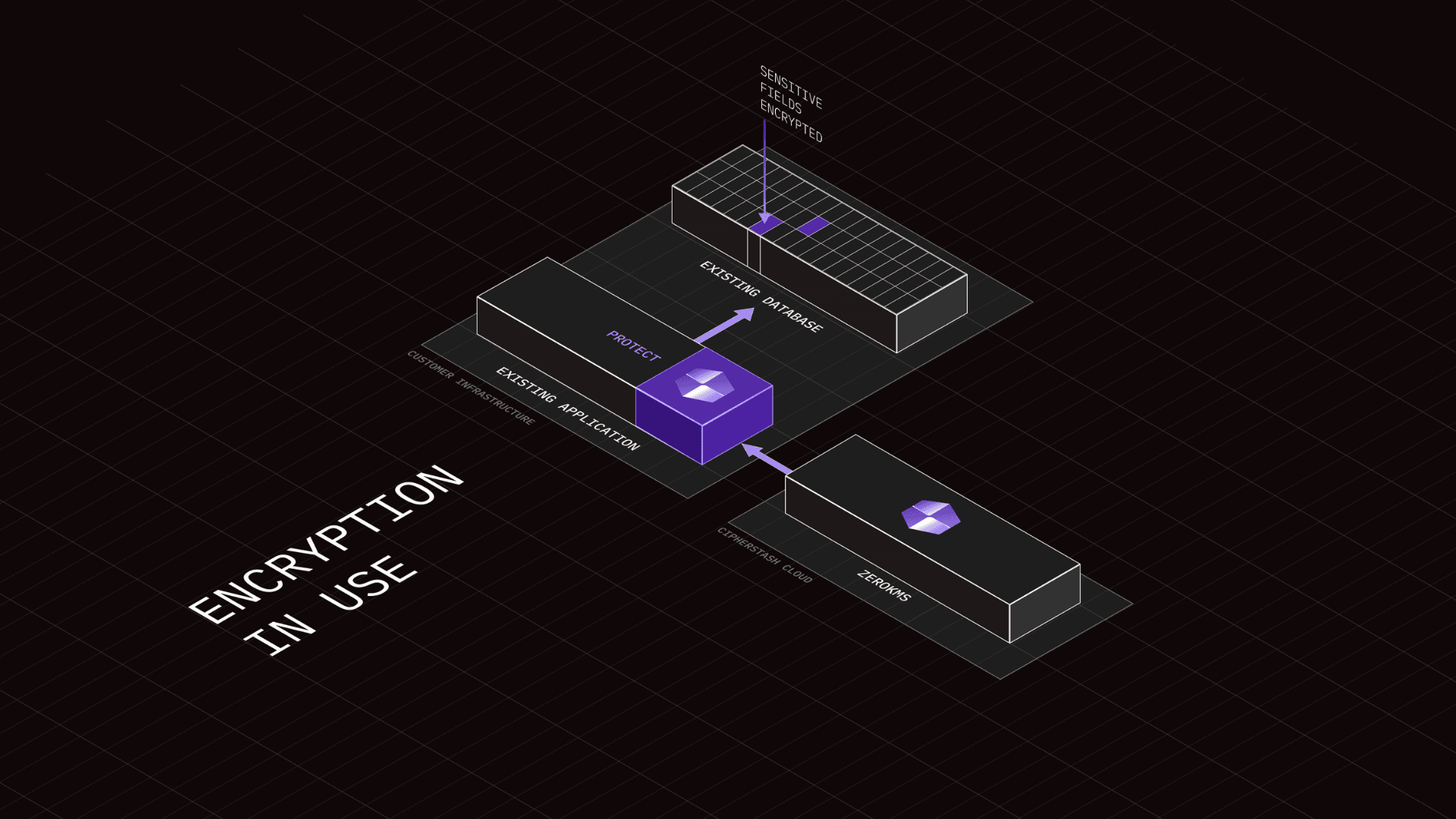
Encryption in use: 3 ways to protect sensitive data in Typescript backends
When building a JavaScript or TypeScript application, few concerns weigh more heavily than the secure handling of sensitive data. Whether you're dealing with personal user information, health records, or simply wanting to follow best practices, implementing data protection is critical.

And now… CipherStash Proxy!
CipherStash Proxy keeps your sensitive data in PostgreSQL encrypted and searchable, without changing your SQL queries. This means that you can protect your most sensitive data with strong security controls, without slowing down your dev team.

Eating your security vegetables – a call for improved cyber hygiene
Exercise, healthy eating, and minimizing alcohol consumption are all preventative measures. We should think of ransomware the same way.
Compliance doesn’t have to be scary
Does the word “compliance” fill you with dread? It doesn’t have to. You probably imagine the time that’s going to be taken away from your important day-to-day work, but as our recent experience at CipherStash shows, there’s another way.

Yay we got SOC 2 for the holidays
Just in time for the end of the year when people are rushing to finish things off, our gift to you is (drumroll please)... SOC 2 compliance!
CipherStash for DynamoDB is generally available
We’re excited to announce general availability of CipherStash for DynamoDB, our cutting-edge solution for client-side data encryption and server-side encrypted search in Amazon DynamoDB.
How can a good developer experience improve your security posture?
Security outcomes are not just delivered by the security team. How can security teams more effectively work with the rest of the business?
Encryption in use with PostgreSQL
Don't just rely on encryption at rest and in transit to protect your sensitive data. Use searchable encryption to enable encryption in use to harden data privacy in Postgres.

Verifying Rust Zeroize with Assembly...including portable SIMD
When writing code that deals with sensitive information like passwords or payment data, it's important to zeroize memory when you're done with it. Failing to do so can leave sensitive in memory even after the program is terminated and even end up on disk when the computer uses swap.

Challenges and Best Practices in Enterprise Data Protection
Large enterprises face especially difficult data protection challenges posed by the scale and diversity of the data they collect and store, the complexity of enterprise organizational structures, the likelihood of facing targeted attacks, and the difficulty in coordinating thousands of employees to move quickly to mitigate risks.

Defining Your Data Governance Strategy for 2024
The effectiveness of your data governance program is determined by how much care and attention you put into the design of its strategy. A well-designed governance strategy sets a sturdy foundation for your framework to click into.

PostgreSQL Security: Best Practices and Tools
PostgreSQL security best practices for access control, password management, logging, and encryption — including the modern CipherStash Stack and Proxy paths for adding searchable, application-level encryption to Postgres.
Let's talk about the Optus hack
Optus just had Australia's biggest ever data breach. Here's what might have happened and how it could have been prevented.
3 security improvements databases can learn from APIs
It turns out there’s heaps we can learn from API security improvements and apply to databases. Here are the top 3!
Cryptographic Failures is now #2 on the OWASP Top 10
The OWASP Top 10 has recently been updated, and it has recognised Cryptographic Failures as the #2 vulnerability category.
CipherStash founder speaks on AusBiz TV
I spoke to host, Sam Brown about why CipherStash could be a gamechanger for enterprise data security.
Welcome David Wu
We are excited to announce that Dr David Wu, Assistant Professor at the University of Virginia, has joined CipherStash as an official advisor
Why we're building CipherStash
With data breaches continuing to threaten our privacy and data security, are current data protection schemes enough?
